Threat Intelligence
6 Lessons from SASE Innovators
How Leading Organizations Are Getting Ahead with Prisma SASE Enterprises have traditionally taken a hardware-based...
What Makes Real Threat Intelligence
First popularized in terminology several years ago, threat intelligence means many things to many people....

Microsoft Digital Defense Report
Over the past year the world has borne witness to a burgeoning cybercrime economy and the rapid rise...

Building the foundation of a mature threat hunting program
Many organizations, especially large global enterprises, don't always have the best visibility into how...
The 7 Hidden Truths of Cloud Security
Based on extensive, up-to-date knowledge and experience from WithSecure consultants, threat hunters and...
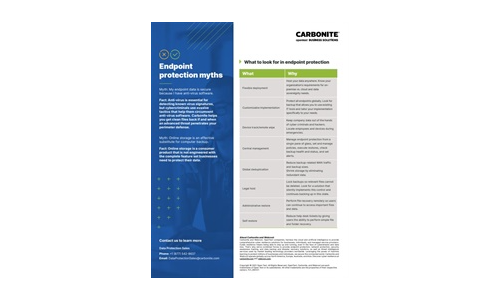
Carbonite Endpoint Protection Myths
Myth: My endpoint data is secure because I have anti-virus software. Myth: Online storage is an effective...
Sign up for Cyber Security Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.