Incident Response
5 Uncomfortable Truths About Phishing Defense
When over 90% of breaches start as phishing emails threats that email gateways miss and other defenses...
Reduce Alert Fatigue in Your IT Environment
Security teams are tasked with managing a huge volume of alert logs, and this noise can overwhelm any...

2022 Cost of Insider Threats: Global Report
Independently conducted by Ponemon Institute External attackers aren't the only threats modern organisations...

Collective Defense: A radar-like view of cyber threats
IronNet is committed to answering the World Economic Forum's call to action for collaborative cyber defense....
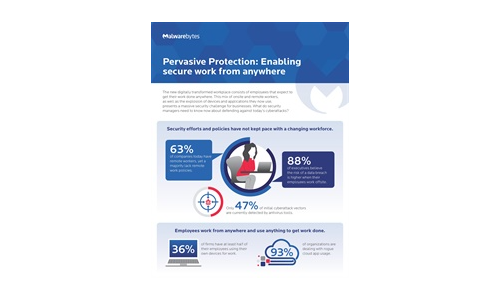
Pervasive Protection: Enabling Secure Work From Anywhere
The new digitally transformed workplace consists of employees that expect to get their work done anywhere....
5 Remote Work Threats and How to Protect Against Them
With the surge in remote work, many IT and security teams are forced to make security tradeoffs to maintain...

2022 Cyber Predictions
The cyber threat landscape has seen great disruptions in 2021 continuing from the pandemic, with the...

Ransomware The True Cost to Business
Ransomware continues to dominate the threat landscape in 2022. Organizations are under siege from a wide...
CMMC Compliance Guide
On January 1, 2020, the United States Department of Defense (DoD) released its Cybersecurity Maturity...

AI Driven Threat Defense The Next Frontier in Cybersecurity
It's undeniable that the landscape of modern cybersecurity has evolved dramatically—and at a rapid...
Sign up for Cyber Security Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.