Firewall

The 4 Benefits of VPN Elimination
The corporate perimeter as you know it no longer exists. Virtual private network (VPN) vulnerabilities...

Raising the Bar for Web App and API Security
Most Web Application and API Security Isn't Enough Securing the web applications and APIs that underpin...
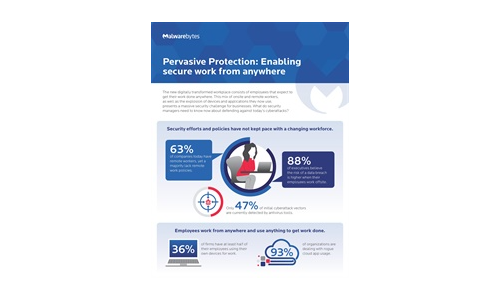
Pervasive Protection: Enabling Secure Work From Anywhere
The new digitally transformed workplace consists of employees that expect to get their work done anywhere....

Modern Blueprint to Insider Threat Management
Taking a People-Centric Approach to Your Insider Threat Management (ITM) Programme Insider threats can...
6 Lessons from SASE Innovators
How Leading Organizations Are Getting Ahead with Prisma SASE Enterprises have traditionally taken a hardware-based...

5 Things You Didn’t Know About DDoS Attacks That Can Cost You
To accurately determine your organization's risk of a DDoS attack, you must be aware of the latest trends...
Cybersecurity Governance for Small and Medium Businesses
Building a foundation to enable cybersecurity governance is key. The cyber threat landscape is constantly...
Hope is NOT a strategy: Secure your business with the Content Cloud
Seems like every week there's news of another security breach. Ponemon Institute has found that the typical...

Farewell ISDN. Hello All-IP.
Analogue and ISDN telephony is a thing of the past – telephony today is mostly internet-based. Voice-over-IP...
Sign up for Cyber Security Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.