Firewall
Remote Access Security checklist for every IT admin
Keep your remote workforce secure and productive. Find everything you need to ensure remote workforce...
7 Insights into Today’s Network Monitoring and Management Approaches
Managing today's complex networks isn't an easy task to navigate. Network operations teams must contend...
The New Era of Fraud: An Automated Threat
Fraudsters employ bots and automated attacks that scour apps looking for any opportunity to hijack business...
The Definitive Email Cybersecurity Strategy Guide
Email is your most essential business tool—and today's top malware delivery vector. This vital communications...
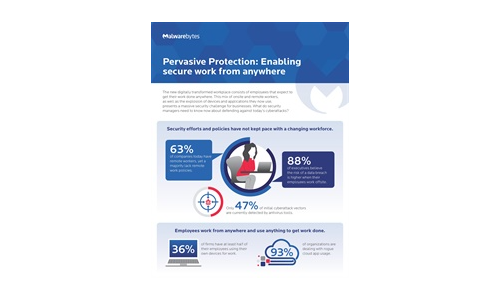
Pervasive Protection: Enabling Secure Work From Anywhere
The new digitally transformed workplace consists of employees that expect to get their work done anywhere....

Building Your MSP Security Offerings
As a managed service provider (MSP), your customers already expect you to keep their networks secure....
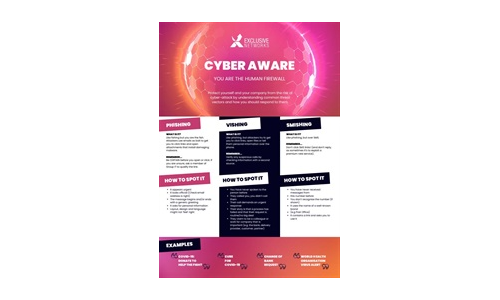
Cyber Aware Infographic
Download this Infographic to see how you can protect yourself and your company from the risk of cyber-attack...
CMMC Compliance Guide
On January 1, 2020, the United States Department of Defense (DoD) released its Cybersecurity Maturity...

Delivering Fast and Secure Enterprise Applications
Adopting a zero trust security model — authenticating and authorizing every request, device, and user...
Back to the Basics: Cyber Hygiene Starts with Asset Management
The challenge: managing millions of dynamic, distributed and diverse assets while maintaining high standards...
Sign up for Cyber Security Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.