Firewall

Insights for SASE Success
5 key considerations to keep in mind As digital transformation drives organizations to consider secure...
Build or Buy? Answering the Eternal Technology Question
The eternal technology question seems to be, “Build or buy?” It is usually posed when a technology...

Modern Blueprint to Insider Threat Management
Taking a People-Centric Approach to Your Insider Threat Management (ITM) Programme Insider threats can...
An Overview of Cato Data Loss Prevention (DLP)
ata is the most valuable asset a modern enterprise has. The evolving threat landscape and shift to cloud...
Delivering Real-time Cloud Security Without Trading Off Performance
There has been a long-standing tradeoff between security and performance, and security often gets the...

2021 Norton Cyber Safety Insights Report Global Results
Prepared by the Harris Poll on behalf of NortonLifeLock, we consider: 1. Cybercrime: Incidence, Impact,...

The 4 Benefits of VPN Elimination
The corporate perimeter as you know it no longer exists. Virtual private network (VPN) vulnerabilities...

AI Driven Threat Defense The Next Frontier in Cybersecurity
It's undeniable that the landscape of modern cybersecurity has evolved dramatically—and at a rapid...

The Evolution of Cybersecurity
Cybersecurity Through the Years As we look at the ever-increasing, technology-dependent cyber environment...
15 Ways Your Website is Under Attack
Web applications are the home of your business on the internet. The functionality within your website,...
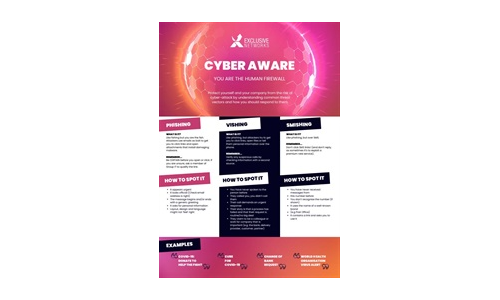
Cyber Aware Infographic
Download this Infographic to see how you can protect yourself and your company from the risk of cyber-attack...
6 Lessons from SASE Innovators
How Leading Organizations Are Getting Ahead with Prisma SASE Enterprises have traditionally taken a hardware-based...
Sign up for Cyber Security Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.