Latest Whitepapers
Pain & Progress: Cybersecurity and Business Risk Study
Despite their best efforts and investments, some organisations still experience difficulty as a result...
A Guide for SMBs: Can I really become “less hackable”?
After nearly 20 years working in cybersecurity, I am still asked the age-old question by business owners:...

Strengthening Critical Infrastructure Security
Advances to critical infrastructure technology is opening the door to threat actors and cyber attacks...

2021 Technology Industry Cyber Threat Landscape Report
The technology industry is a top target for both cybercriminals and state-sponsored cyber espionage groups....
Reduce Alert Fatigue in Your IT Environment
Security teams are tasked with managing a huge volume of alert logs, and this noise can overwhelm any...

Elastic Cloud Gateways: The Evolution of Secure Cloud Access
Enterprise security groups today face a daunting task. While their core responsibility of protecting...
NERC CIP Best Practices: The Tripwire Approach
Industrial operators beholden to the North American Electric Reliability Corporation Critical Infrastructure...

BlackBerry Cyber Suite
The challenge of securing and protecting data and endpoints is not a new requirement, but today it is...
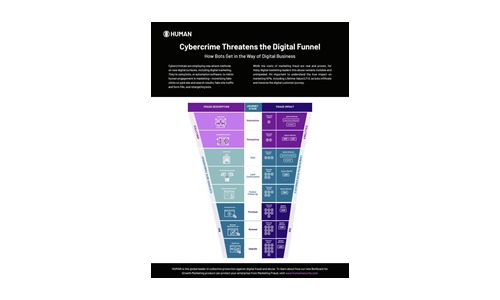
Cybercrime Threatens the Digital Funnel
Cybercriminals are employing new attack methods on new digital surfaces, including digital marketing....

Introducing a Cyber Security Service For Home WiFi
The renewal cycle for home WiFi routers is lengthy and involves users upgrading to a newer model once...
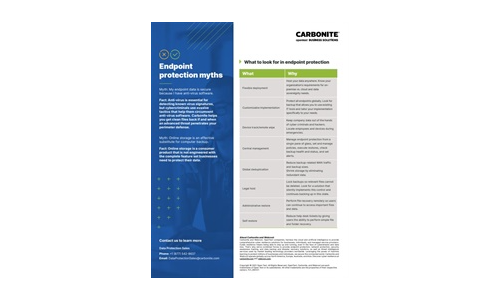
Carbonite Endpoint Protection Myths
Myth: My endpoint data is secure because I have anti-virus software. Myth: Online storage is an effective...
PhishBusters Survey: Perception vs. Reality of Phishing Attacks
Cofense conducted a survey to examine the general public's perceptions of phishing attacks, including...
NAIKON: Traces from a Military Cyber-Espionage Operation
NAIKON is a threat actor that has been active for more than a decade. The group focuses on high profile...
Sign up for Cyber Security Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.