Endpoint Protection
Ransomware Case Studies
Ransomware is a simple name for a complex collection of security threats. Attacks can be short and brutal,...

The Evolution of Cybersecurity
Cybersecurity Through the Years As we look at the ever-increasing, technology-dependent cyber environment...

How Secure is your Cloud data
With employees working remotely at higher rates, business data is increasingly at risk. IT administrators...
Remote Access Security checklist for every IT admin
Keep your remote workforce secure and productive. Find everything you need to ensure remote workforce...
Lessons from REvil’s Return
Ransomware is not just another buzzword. It is a very real threat to businesses and educational institutions...
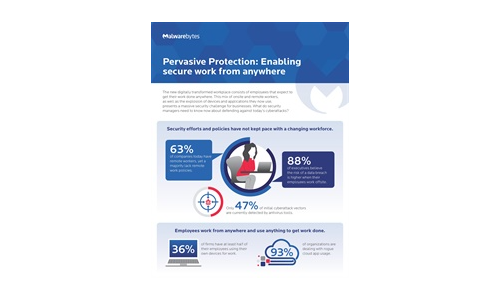
Pervasive Protection: Enabling Secure Work From Anywhere
The new digitally transformed workplace consists of employees that expect to get their work done anywhere....
Build or Buy? Answering the Eternal Technology Question
The eternal technology question seems to be, “Build or buy?” It is usually posed when a technology...
Six Steps to Successful and Efficient Threat Hunting
Rather than waiting for an alert, threat hunters proactively assume that an advanced adversary operates...

5 Benefits of Partnering with Webroot
While cyberattacks continue to evolve in volume, organization, and sophistication, security technology...
Back to the Basics: Cyber Hygiene Starts with Asset Management
The challenge: managing millions of dynamic, distributed and diverse assets while maintaining high standards...
12 Steps for Stronger Ransomware Protection
Over the last few years, we have signed up hundreds of MSPs. We like to ask every new customer why they...
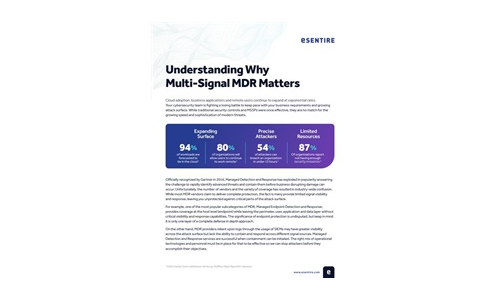
Understanding Why Multi-Signal MDR Matters
MDR providers can only detect and respond to what they can see. A multi-signal approach is paramount...

Multi-Vector Protection
Educating users is an undeniably effective way to protect them from phishing and other malware, but it...

BlackBerry Cyber Suite
The challenge of securing and protecting data and endpoints is not a new requirement, but today it is...
Sign up for Cyber Security Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.

