Email Security
A Visual Landscape Of Cybersecurity
Our world has never moved faster in terms of cyber threats, security technology innovations and overall...
A Guide for SMBs: Can I really become “less hackable”?
After nearly 20 years working in cybersecurity, I am still asked the age-old question by business owners:...
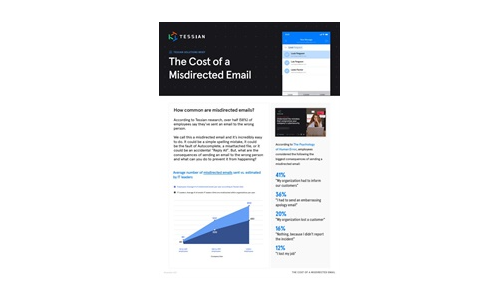
What is the Cost of a Misdirected Email?
The average number of misdirected emails is almost always higher than IT leaders estimate, making it...
Drive Real Behaviour Change
Cybersecurity awareness training is one of the most important things you can do to secure your organisation....

Six Signs Your Email Gateway Might Need Replacing
Many organisations are spending way too much money on licensing the their email SPAM and malware gateway...

Cloud Adoption and Risk Report
The recent work from home mandate has dramatically changed how we live and work. Organisations are getting...
Bridging the Gap of Grief with Business-Driven Security
Worldwide spending on information security products and services will reach $86.4 billion in 2017, an...
2022 Annual State of Phishing Report
Enriched with robust threat intelligence from the Cofense Phishing Defense Center (PDC), which analyzes...
Essential How-To Guide: Prevent Accidental Emailing
NO ORGANIZATION IS IMMUNE TO HUMAN ERROR In this e-book you'll get a closer look at data breaches and...

Microsoft Digital Defense Report
Over the past year the world has borne witness to a burgeoning cybercrime economy and the rapid rise...
Zero Trust Privilege for dummies
Cyber breaches are bigger and worse than ever. Hardly a day goes by without headlines about some new...

Secure Email Gateway: Buyer’s Guide
Protecting your organization against email-borne threats is only becoming more difficult as attackers...
Modern Networking for the Borderless Enterprise
5 Ways Top Organizations Are Optimising Networking at the Edge. Enterprises are growing more dispersed...
Sign up for Cyber Security Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.