Latest Whitepapers

Introducing a Cyber Security Service For Home WiFi
The renewal cycle for home WiFi routers is lengthy and involves users upgrading to a newer model once...

PCI Compliance Best Practices
The Payment Card Industry Data Security Standard (PCI DSS) has been in place since 2004, with the latest...

2022 Cyberthreat Defense Report
Interested in strengthening your cybersecurity strategy? Each year, CyberEdge provides a comprehensive...
15 Ways Your Website is Under Attack
Web applications are the home of your business on the internet. The functionality within your website,...
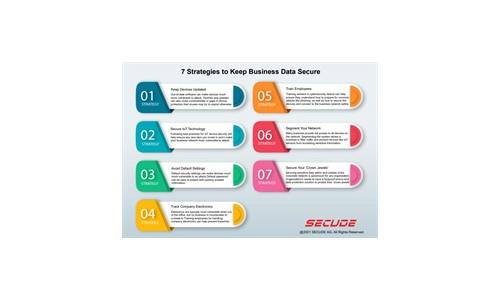
7 Strategies to Keep Business Data Secure
Read our simple infographic which headlines seven strategies to keep your business data secure. ...
CMMC Compliance Guide
On January 1, 2020, the United States Department of Defense (DoD) released its Cybersecurity Maturity...
Lay the Foundation for Zero Trust
Zero Trust has been a topic of discussion in the Federal Government for some time. However, the approach...

The Cost of ‘Good Enough’ Security ebook
Investing in cybersecurity technologies is one strategy for reducing cyber risk. But how can you be confident...
Edging Towards SASE: Next generation networking, cloud and security
The global pandemic has delivered a paradigm shift in the relationship between employees and their workplace....
Open Channels, Hidden Threats
How Communication and Social Media Tools Are Changing the Insider Risk Equation for Compliance, IT and...
An Integrated Approach to Embedding Security into DevOps
Organizations are adopting DevOps as a development and operational model to facilitate the practice of...
Sign up for Cyber Security Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.