Encryption
5 Best Practices for Securing Modern Web Applications and APIs
Web applications are nothing new. Neither is web application security. Many businesses have been building...

The Evolution of Cybersecurity
Cybersecurity Through the Years As we look at the ever-increasing, technology-dependent cyber environment...
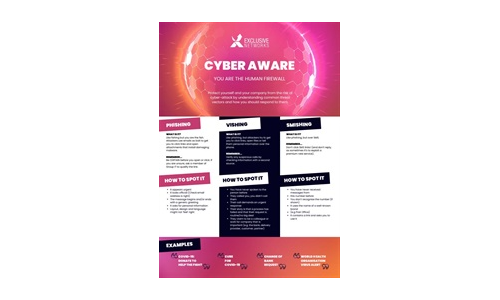
Cyber Aware Infographic
Download this Infographic to see how you can protect yourself and your company from the risk of cyber-attack...
Zero Trust Privilege for dummies
Cyber breaches are bigger and worse than ever. Hardly a day goes by without headlines about some new...
Cloud Security Report 2022
Cloud adoption continues to permeate throughout organizations as they embrace agile software development....

Your Path to Zero Trust
In a business world without perimeters and dominated by remote work, finding a balance between easy collaboration...
Hope is NOT a strategy: Secure your business with the Content Cloud
Seems like every week there's news of another security breach. Ponemon Institute has found that the typical...

10 Security Tips for Businesses
SECURITY THAT PROTECTS YOUR BUDGET Vanishing budgets, reckless users, infected machines, unpatched software...

Stopping Ransomware: Dispatches from the Frontlines
No organization wants to discover a ransomware attack unfolding in their environment, but if you can...

Social Engineering Handbook: How to Take the Right Action
The aim of this handbook is to help introduce social engineering and its risks to every employee in the...
CRM Evolved Introducing the Era of Intelligent Engagement
Digital Transformation, a key focus of successful organizations, proves itself a business imperative,...
NAIKON: Traces from a Military Cyber-Espionage Operation
NAIKON is a threat actor that has been active for more than a decade. The group focuses on high profile...
Sign up for Cyber Security Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.